Windows Server 2003 includes another mechanism for deploying security configuration settings called security templates. A security template
is a collection of configuration settings stored as a text file with
the .inf extension. A security template contains many of the same
security parameters discussed in the previous lessons, and it presents
them in a unified interface that enables you to save your configurations
as files and deploy them when and where they are needed. In this
lesson, you will learn about security templates and the methods you can
use to apply them, including deployment to multiple computers through
Group Policy, scripted deployments, and analysis of a computer’s
existing security configuration.
Understanding Security Templates
Security templates
consist of policies and settings you can use to control a computer’s
security configuration using local policies or group policies. You can
use security templates to configure any of the following types of
policies and parameters:
Account Policies Enables you to specify password restrictions, account lockout policies, and Kerberos policies
Local Policies Enables you to configure audit policies, user rights assignments, and security options policies
Event Log policies Enables you to configure maximum event log sizes and roll-over policies
Restricted Groups Enables you to specify the users who are permitted to be members of specific groups
System Services Enables you to specify the startup types and permissions for system services
Registry permissions Enables you to set access control permissions for specific registry keys
File System permissions Enables you to specify access control permissions for NTFS files and folders
You can deploy
security templates in a variety of ways, using Active Directory
directory service Group Policy Objects, the Windows Server 2003 Security
Configuration And Analysis snap-in, or the Secedit.exe command-line
utility. When you associate a security template with an Active Directory
object, the settings in the template become part of the GPO associated
with the object. You can also apply a security template directly to a
computer, in which case the settings in the template become part of the
computer’s local policies.
There are several
advantages to storing your security configuration parameters in security
templates. Because the templates are plain text files, you can work
with them manually as with any text file, cutting and pasting sections
as needed. Second, templates make it easy to store security
configurations of various types so that you can easily apply different
levels of security to computers performing different roles.
Tip
Storing
your security settings in templates also provides an adequate backup of
a computer’s security configuration that you can use to quickly and
easily restore the system to its original configuration. For example,
when working with GPOs, it is easy to forget what changes you have made,
and manually restoring the GPO to its original configuration can be
difficult. If you have a security template containing your original
settings, you can simply apply it to the GPO to return to your default
settings. |
Using the Security Templates Snap-in
To work with security
templates, you use the Security Templates snap-in. By default, the
Windows Server 2003 Administrative Tools folder does not include an MMC
console with the Security Templates snap-in, so you have to create one
yourself using the MMC Add/Remove Snap-in function. When you do this,
the console provides an interface like the one shown in Figure 1.
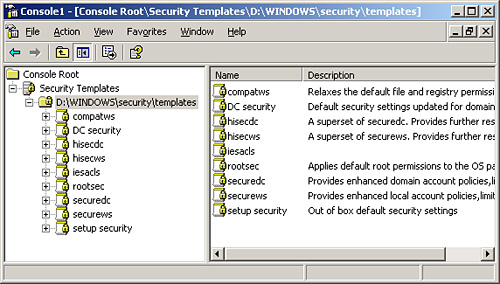
The
scope pane of the Security Templates snap-in contains a list of all the
template files the program finds in the Windows\Security\Templates
folder on the system drive. The snap-in interprets any file in this
folder that has an .inf extension as a security template, even though
the extensions do not appear in the console.
Tip
You
can add security templates in other folders to the console by selecting
New Template Search Path from the Action menu and then browsing to the
folder containing your templates. Please note, however, that not all the
files with .inf extensions on a computer running Windows Server 2003
are security templates. The operating system uses files with .inf
extensions for other purposes as well. |
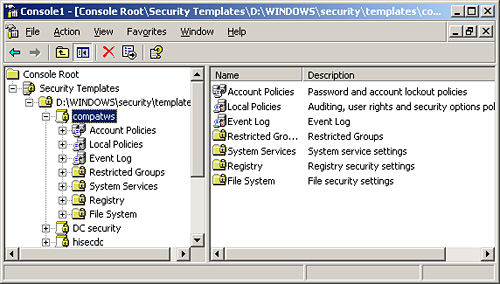
When you expand one of the
templates in the scope pane, you see a hierarchical display of the
policies in the template (as shown in Figure 2),
as well as their current settings. You can modify the policies in each
template just as you would using the Group Policy Object Editor console.
Default Security Templates
Windows
Server 2003 includes a selection of predefined security templates you
can use as is or modify to your needs. These templates provide different
levels of security for servers performing specific roles. The
predefined templates are located in the Windows\Security\Templates
folder unless otherwise noted:
Setup Security.inf
Contains the default security settings created by the Windows Server
2003 Setup program. The settings in the template depend on the nature of
the installation, such as whether it was an upgrade or a clean install.
You can use this template to restore the original security
configuration to a computer you have modified.
Important
When
you use a security template to restore a computer’s default settings,
remember that the template might overwrite existing permissions modified
by the installation of other applications. After you restore the
default settings, you might have to reinstall your applications or
modify certain file system or registry permissions manually. |
DC Security.inf
A computer running Windows Server 2003 creates this template only when
you promote the computer to a domain controller. The template contains
the default file system and registry permissions for domain controllers,
as well as system service modifications.
Caution
The
Setup Security.inf and DC Security.inf templates contain a large number
of settings, and in particular a long list of file-system permission
assignments. For this reason, you should not apply these templates to a
computer by using group policies. Computers running Microsoft Windows
operating systems periodically refresh group policy settings by
accessing the GPOs on the network’s domain controllers, and a template
of this size can generate a great deal of Active Directory traffic on
the network. Instead of using group policies, you should apply the
template using the Security Configuration And Analysis snap-in or the
Secedit.exe utility. |
Securedc.inf
This template contains policy settings that increase the security on a
domain controller to a level that remains compatible with most functions
and applications. The template includes more stringent account
policies, enhanced auditing policies and security options, and increased
restrictions for anonymous users and LAN Manager systems.
Hisecdc.inf
This template contains policy settings that provide an even greater
degree of security for domain controllers than the Securedc.inf
template. Applying this template causes the computer to require
digitally signed communications and encrypted secure channel
communications instead of just requesting it, as Securedc.inf does. This
template also adds registry and file security, removes all members from
the Power Users group, and disables additional services.
Compatws.inf
By default, the members of the local Users group on a computer running a
Windows operating system can run only applications that meet
requirements of the Designed For Windows Logo Program For Software. To
run applications that are not compliant with the program, a user must be
a member of the Power Users group. Some administrators want to grant
users the ability to run these applications without giving them all the
privileges of the Power Users group. The Compatws.inf template modifies
the default file system and registry permissions for the Users group,
enabling the members to run most applications, and also removes all
members from the Power Users group.
Caution
The
Compatws.inf template is not intended for domain controllers, so you
should not link it to a site, to the domain, or to the Domain
Controllers OU. |
Securews.inf
This template contains policy settings that increase the security on a
workstation or member server to a level that remains compatible with
most functions and applications. The template includes many of the same
account and local policy settings as Securedc.inf, and it implements
restrictions on LAN Manager, digitally signed communications and greater
anonymous user restrictions.
Hisecws.inf This
template contains policy settings that provide higher security than
Securews.inf on a workstation or member server. In addition to having
many of the same settings as Hisecdc.inf, this template increases
security for NTLM, removes all members from the Power Users group, and
makes the Domain Admins group and the local Administrator account the
only members of the local Administrators group.
Tip
The
Securedc.inf, Securews.inf, Hisecdc.inf, and Hisecws.inf templates are
all designed to build on the default Windows security settings, and they
do not themselves contain those default settings. If you have modified
the security configuration of a computer substantially, you should first
apply the Setup Security.inf template (and the DC Security.inf template
as well, for domain controllers) before applying one of the secure or
highly secure templates. |
Rootsec.inf
This template contains only the default file system permissions for the
system drive on a computer running Windows Server 2003. You can use
this template to restore the default permissions to a system drive that
you have changed, or to apply the system drive permissions to the
computer’s other drives.
Iesacls.inf This template applies registry permissions on keys integral to Microsoft Internet Explorer.
Modifying Security Templates
To create a baseline security policy, you might want to modify the predefined templates.
Tip
If
you want to make changes to any of the policies in the predefined
templates, you should make a backup copy of the template file first to
preserve its original configuration. You can copy a template by simply
copying and pasting the file in the normal manner using Microsoft
Windows Explorer, or you can use the Security Templates snap-in by
selecting a template and, from the Action menu, choosing Save As and
supplying a new file name. |
Use the Security Templates snap-in to modify security templates by following these steps:
1. | Using Windows Explorer, create a new folder for custom templates.
|
2. | Copy a predefined template into the new folder to create a custom baseline template.
|
3. | Create a console with the Security Templates snap-in.
|
4. | Add the new folder location to the template search path.
|
5. | Modify the custom template.
|
6. | Save the template.
|
7. | If necessary, modify a template by editing its .inf file.
|
Tip
You
should add most template settings using the Security Templates snap-in.
The template file is a text file, but the required syntax might be
confusing, and using the snap-in ensures that settings are changed using
the proper syntax. However, the exception to this rule is adding
Registry settings that are not already listed in the Security Option
portion of the template. As new security settings become known, if they
can be configured using a Registry key, you can add them to a security
template. To do so, you add them to the [Registry Values] section of the
template. The article “How to Add Custom Registry Settings to Security
Configuration Editor” helps you understand how to perform this task. You
can find it at http://support.microsoft.com/?kbid=214752. |
Deploying Security Templates Using Group Policy Objects
Creating and
modifying security templates does not improve security unless you apply
those templates. To configure a large group of computers in a single
operation, you can import a security template into the Group Policy
Object for a domain, site, or organizational unit object in Active
Directory. However, there are a few cautions that you must observe when
using group policies to deploy security templates.
Group Policy Deployment Cautions
As with other
security settings, the configuration parameters you import into the
Group Policy Object for a specific container are inherited by all the
objects in that container, including other containers. Most networks use
different levels of security for computers performing various roles, so
it is relatively rare for administrators to apply a security template
to a domain or site object—because then all the computers in that domain
or site receive the same settings. At the very least, your domain
controllers should have a higher level of security than the other
computers on your network.
Tip
When
creating security templates for deployment via GPOs, the best practice
is to place your computers into organizational units according to their
roles and create individual security templates for each OU. This way you
can customize the security configuration for each role and modify the
template for each role as needed, without affecting the others. |
Another
consideration when importing security templates into Group Policy
Objects is the amount of data in the template itself. Every computer
running a Windows operating system in an Active Directory container
refreshes its Group Policy settings at a regular interval, by default
every 16 hours, even if the GPOs have not been modified. A security
template can contain a large number of settings, and the continual
refreshing of large templates to a large fleet of computers could
generate a great deal of Active Directory traffic and place a heavy
burden on the network’s domain controllers.
Note
When
you look at the sizes of the predefined security templates included
with Windows Server 2003, you can easily see which ones you should not
deploy using group policies. Most of the templates are less than 10
kilobytes, with the notable exceptions of the DC Security.inf and Setup
Security.inf templates, which are 127 and 784 kilobytes, respectively. |
Importing Security Templates into GPOs
To deploy a security
template using group policies, you select an Active Directory object
that has a GPO and import the template into the GPO. The template’s
settings then become part of the GPO, overwriting any existing values.
The importation process proceeds as follows:
1. | Open the Active Directory Users And Computers console.
|
2. | Select
the domain or organizational unit object to which you want to apply the
template and, from the Action menu, choose Properties. The Properties
dialog box for that object appears.
|
3. | Click
the Group Policy tab, select a Group Policy Object from the Group
Policy Object Links list, and then click Edit. The Group Policy Object
Editor console appears.
Tip Instead
of using an existing Group Policy Object, you can also create a new one
by clicking New and then supplying a name for the GPO. |
|
4. | Under Computer Configuration, expand the Windows Settings subheading, and then click Security Settings.
|
5. | From the Action menu, select Import Policy. The Import Policy From dialog box appear.
|
6. | Select
the security template file you want to import, and then click Open. The
settings in the template are imported into the Group Policy Object.
|
7. | Close the Group Policy Object Editor console, and then click OK in the Properties dialog box for the object you selected.
|
8. | Close the Active Directory Users And Computers console. |